In this edition, we will focus on the patches by Microsoft, Adobe, Apple Cisco, and SAP.
There have been three major zero-day exploits identified, with two of these known to have been actively exploited in the wild
Microsoft
In their May Patch Tuesday release, Microsoft has addressed 61 vulnerabilities, with only one of those rated as Critical and 2 being zero-day vulnerabilities. The patches cover a broad array of applications and services, including Windows, SharePoint, Visual Studio, Intune, Office, PowerBI, .Net, and more. Additionally, there has been one Edge/Chromium based vulnerability identified; this is known to have been exploited in the wild, although it has been patched in the latest release of Edge/Chromium.
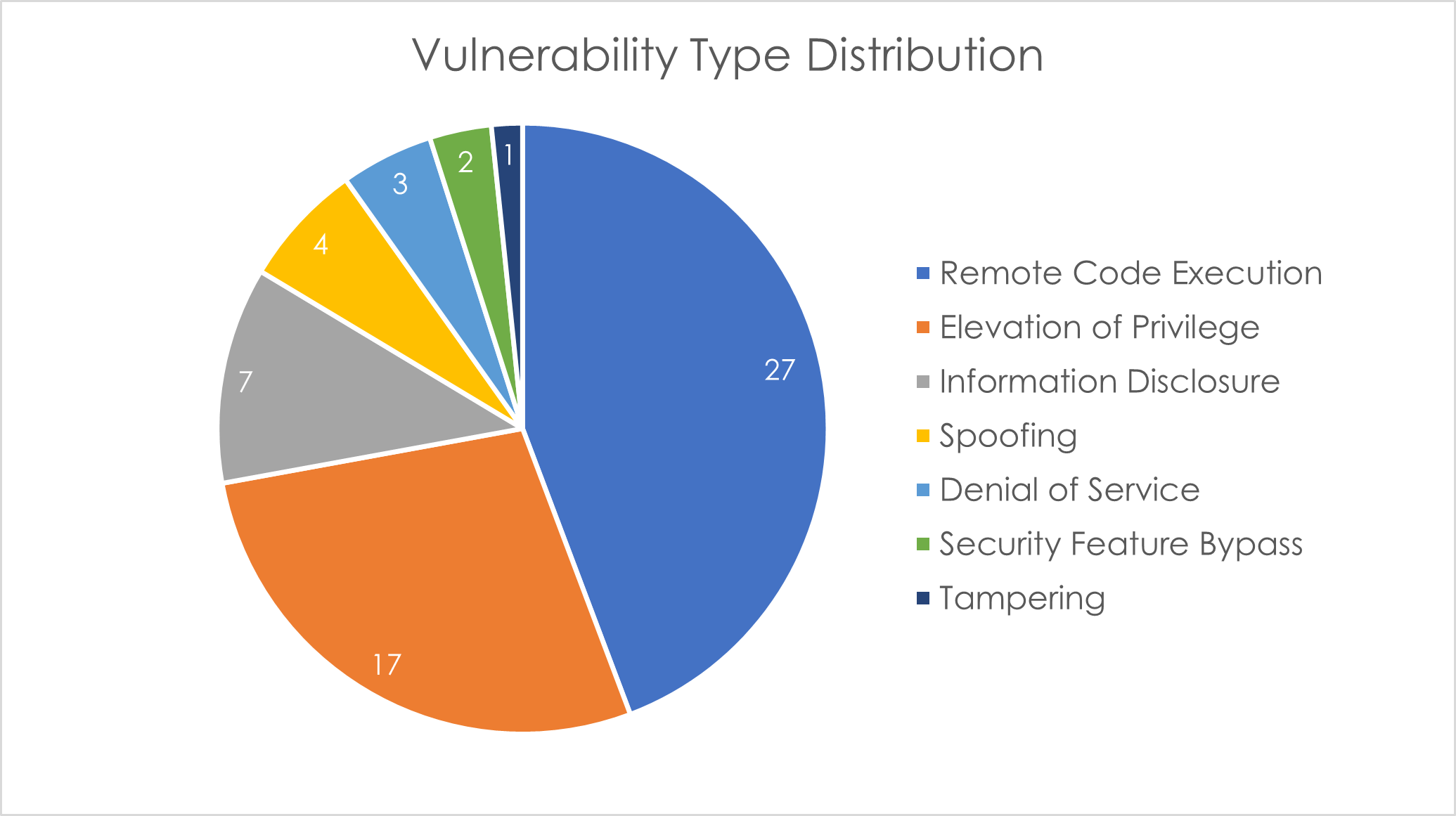
This month's vulnerabilities chiefly revolve around Remote Code Execution (RCE), Elevation of Privilege (EoP), and Information Disclosure.
Outlined below are the two Microsoft zero-day vulnerabilities detailed in this month’s Patch Tuesday, as well as the one critical:
Zero-days
1. CVE-2024-30040 – This is a Security Feature Bypass vulnerability in Windows MSHTML that can allow an attacker to bypass OLE mitigations in Microsoft 365 and Microsoft Office, which protect users from vulnerable COM/OLE controls. It is rated as Important, and has a CVSS score of 8.8. Users must interact with a malicious file, which doesn't require them to explicitly open or click the file but manipulate it possibly through an enticement in an Email or Instant Messenger message. An unauthenticated attacker could exploit this by convincing a user to open a malicious document, which would then execute arbitrary code within the user’s security context. This vulnerability is known to have been exploited in the wild, therefore users should look to patch this vulnerability as soon as possible to prevent potential exploitation.
2. CVE-2024-30051 – This is a Heap-based Buffer Overflow vulnerability in Windows DWM Core Library that can allow an attacker to elevate privileges to SYSTEM level. This vulnerability was identified in the wild by Kaspersky, DBAPPSecurity WeBin Lab, and Google (Threat Analysis Group and Mandiant). It is rated as Important, and has a CVSS score of 7.8. Although it is only rated as Important, it is known to have been exploited in the wild, and users should look to patch this vulnerability as soon as possible to prevent potential exploitation. No specific user interaction is required for exploitation, making it particularly severe.
Critical
1. CVE-2024-30044 – This is a Remote Code Execution (RCE) vulnerability in Microsoft SharePoint Server that can allow an attacker to leverage a Deserialization of Untrusted Data weakness. This vulnerability is particularly severe, having been rated as Critical (CVSS 8.8) and noted to be “Exploitation More Likely”. An authenticated attacker, requiring low-level privileges as a Site Owner, can upload a specially crafted file to SharePoint Server and manipulate API requests to trigger deserialization of the file’s parameters, resulting in the execution of arbitrary code in the context of the SharePoint Server. Although the exploit code maturity is unproven, the potential for remote code execution means that users should look to patch this vulnerability as soon as possible to prevent potential exploitation.
Adobe
Adobe has released eight patches this month addressing 37 vulnerabilities, 50% more last month. The applications in question are:
Acrobat and Reader – 9 Critical and 2 Important
Animate – 6 Critical and 1 Important
FrameMaker – 5 Critical and 3 Important
Substance3D Painter – 2 Critical and 2 Important
Illustrator – 2 Critical and 1 Important
Aero – 1 Critical
Dreamweaver – 1 Critical
Substance3D Designer – 1 Important
All of these vulnerabilities are rated as a priority 3 by Adobe, meaning they relate to a product that has historically not been a target for attackers.
Apple
Apple has recently released security updates for the majority of their operating systems including:
· Safari
· iOS and iPadOS
· MacOS
· watchOS
· tvOS
·iTunes
Cisco
Cisco has released 7 advisories for 9 vulnerabilities since last month’s patch Tuesday, with the impact ratings ranging from Medium to High. There are no critical advisories this month, however the majority of the advisories relate to Cisco ASA, Integrated Management Controller, IOS, and Cisco IP Phones.
SAP
SAP has released 14 new security notes and 3 updates to previous security notes. Four of these CVEs are rated “High” or “Hot News” (Very High). The products affected by the high to very high rated CVEs are:
· SAP Business Client (CVSS 10.0)
· SAP Commerce (CVSS 9.8)
· SAP NetWeaver Application Server ABAP and ABAP Platform (CVSS 9.6)
· SAP BusinessObjects (CVSS 8.1)
Industrial Control Systems
Any customers utilising industrial control systems (ICS) should be aware of three security advisories regarding
ICSA-24-130-01 Rockwell Automation FactoryTalk Historian SE
ICSA-24-130-02 alpitronic Hypercharger EV Charger
ICSA-24-130-03 Delta Electronics InfraSuite Device Master
ICSA-24-107-03 Rockwell Automation ControlLogix and GuardLogix (Update A)
ICSA-24-128-01 PTC Codebeamer
ICSA-24-128-02 SUBNET Substation Server
Defending OT Operations Against Ongoing Pro-Russia Hacktivist Activity
CISA have also published a fact sheet providing information and mitigations associated with cyber operations conducted by pro-Russia hacktivists who seek to compromise industrial control systems (ICS) and small-scale operational technology (OT) systems in North American and European critical infrastructure sectors, including Water and Wastewater Systems, Dams, Energy, and Food and Agriculture Sectors.
As always, users are recommended to install the latest security updates as soon as possible to protect their systems from potential threats.




