Microsoft
In their June Patch Tuesday release, Microsoft has addressed 51 vulnerabilities, with only one of those rated as Critical. Interestingly there is also only one publicly disclosed zero-day, and this is not the previously mentioned ‘Critical’ vulnerability. The patches cover a broad array of applications and services, including Visual Studio, Windows, Azure (including the SDK), Office
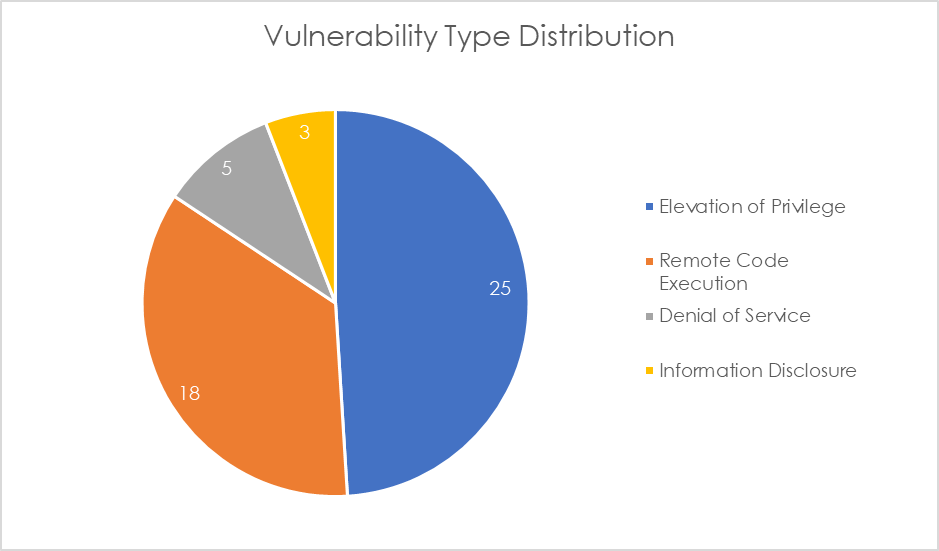
This month's vulnerabilities chiefly revolve around Elevation of Privilege (EoP), Remote Code Execution (RCE), and Denial-of-Service (DoS).
Outlined below are the zero-day and critical vulnerabilities detailed in this month’s Microsoft patch update:
Critical
1. CVE-2024-30080 – This is a Remote Code Execution vulnerability in Microsoft Message Queuing (MSMQ) that can allow an attacker to execute arbitrary code on the server side. Given its high potential impact on confidentiality, integrity, and availability, it is rated as Critical with a CVSS score of 9.8. Although the exploit code maturity is currently unproven, meaning active exploitation is not confirmed, users are advised to apply patches immediately. The vulnerability can be exploited by sending a specially crafted malicious MSMQ packet to an MSMQ server where the messaging service is enabled and listening on TCP port 1801.
Zero-day
1. CVE-2023-50868 – This is a Denial-of-Service vulnerability in DNSSEC validation that can allow an attacker to exhaust CPU resources on a DNS resolver, effectively causing service disruption for legitimate users. Although this had been publicly disclosed, it has only been rated as Important, with a CVSS score of 7.5 and noted as “Exploitation less likely”. This vulnerability was previously disclosed in February and patched in multiple DNS implementations including BIND, PowerDNS, Unbound, Knot Resolver, and dnsmasq. As always, users should try to apply all patches where possible.
Adobe
Adobe has released 10 security updates this month, addressing 64 vulnerabilities – almost double the number of vulnerabilities as last month. The applications in question are:
Commerce – 7 Critical and 3 Important
FrameMaker Publishing Server – 2 Critical
Experience Manager – 1 Critical and 42 Important (1 mod)
Creative Cloud Desktop – 1 Critical
Photoshop – 1 Critical
Substance 3D Stager – 1 Critical
Acrobat Android - 2 Important
Audition – 2 Important
ColdFusion – 2 Important
Media Encoder – 1 Important
All of these vulnerabilities are rated as a priority 3 by Adobe, meaning they relate to a product that has historically not been a target for attackers.
Check Point
Check Point has released one advisory in June, which is an update to a vulnerability previously disclosed in May.
The vulnerability in question is CVE-2024-24919 – This is an information disclosure vulnerability in Check Point VPN. Identified in various versions of Check Point Quantum Gateway and CloudGuard Network, including R81.20, R81.10, R81, and R80.40, as well as Check Point Spark versions R81.10 and R80.20, this issue could allow a remote attacker to access sensitive information. Due to the vulnerability's nature and potential impact, it has been rated as High severity. Users are urged to apply the latest updates to ensure that this is patched.
Cisco
Cisco has so far released two advisories for two vulnerabilities in June, with the impact ratings ranging from Informational to Medium. The Medium rated vulnerabilities both relate to Cisco Finesse.
Fortinet
Fortinet has addressed five vulnerabilities in June: one High, three Medium, and one Low severity.
The High severity vulnerability is CVE-2024-23110 – this is a stack-based buffer overflow vulnerability in the command line interpreter of FortiOS that can allow an authenticated attacker to execute unauthorised code or commands via specially crafted command line arguments. Identified as CWE-121, this issue affects multiple versions across several FortiOS branches. Users are strongly recommended to upgrade their systems to the patched versions provided by Fortinet to mitigate this risk where possible.
SAP
SAP has released 10 new security notes and 3 updates to previous security notes. Only two of these CVEs are rated “High” or “Hot News” (Very High). The products affected by the high to very high rated CVEs are:
- SAP Financial Consolidation
- SAP NetWeaver AS Java
Industrial Control Systems
Any customers utilising industrial control systems (ICS) should be aware of multiple security advisories relating to the following systems:
- ICSA-24-163-01 Rockwell Automation ControlLogix, GuardLogix, and CompactLogix
- ICSA-24-163-02 AVEVA PI Web API
- ICSA-24-163-03 AVEVA PI Asset Framework Client
- ICSA-24-163-04 Intrado 911 Emergency Gateway
- ICSA-23-108-02 Schneider Electric APC Easy UPS Online Monitoring Software (Update A)
- ICSMA-24-163-01 MicroDicom DICOM Viewer
As always, users are recommended to install the latest security updates as soon as possible to protect their systems from potential threats.




