There have been a number of zero-day exploits identified, with many of these known to have been actively exploited in the wild.
Microsoft
In their December Patch Tuesday release, Microsoft has addressed 71 vulnerabilities, with 16 of those rated as Critical. There has been only one zero-day vulnerability detailed this month, the lowest in six months (since June).
The patches cover a broad array of applications and services, including Remote Desktop Services, common Windows services, basically the full Microsoft Office stack, Windows kernel and associated drivers, Defender for Endpoint, LDAP and more. (.NET is conspicuously absent this month!)
Additionally, there have been 2 Edge/Chromium based vulnerabilities identified, although no advisory notes have been issued.
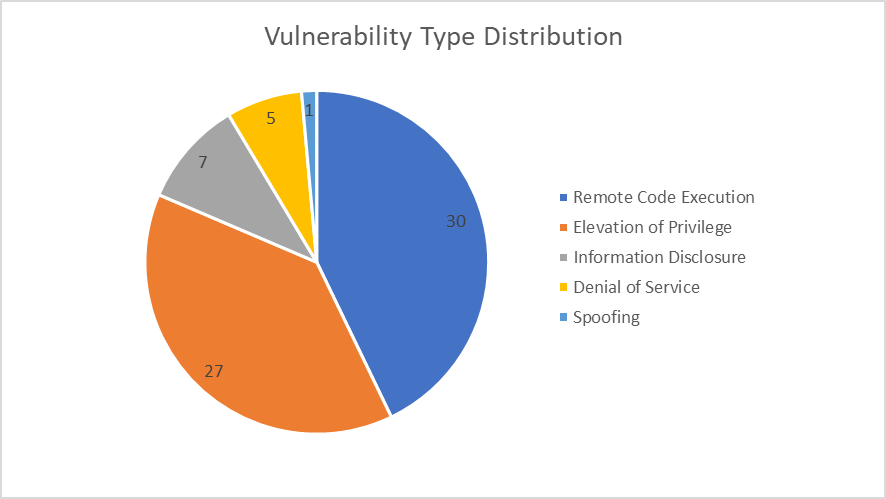
This month's vulnerabilities chiefly revolve around Remote Code Execution (RCE), Elevation of Privilege (EoP), and Information Disclosure.
There are two main focuses for this Patch Tuesday, the actively exploited zero-day and the slew of critical RCE vulnerabilities in Remote Desktop Services:
Zero-day
CVE-2024-49138 – This is a Heap-based Buffer Overflow vulnerability in the Windows Common Log File System Driver that can allow an attacker to elevate privileges to SYSTEM level. It is rated as Important and has a CVSS score of 7.8. The vulnerability requires low privileges and no user interaction, and it has been publicly disclosed and exploited. Since this is known to have been exploited in the wild, users should look to patch this vulnerability as soon as possible to prevent potential exploitation. Official fixes have been issued for various Windows versions to address this vulnerability.
Remote Desktop Services
All the critical RCE vulnerabilities in Remote Desktop Services published today share a number of similarities: they have identical CVSS vectors, exploitation requires that an attacker win a race condition, and the same research group is credited in each case.
Nine are rated as critical and two as important: CVE-2024-49115, CVE-2024-49116, CVE-2024-49123, CVE-2024-49129, CVE-2024-49075, CVE-2024-49128, CVE-2024-49128, CVE-2024-49106, CVE-2024-49108, CVE-2024-49119, CVE-2024-49120.
Adobe
Adobe has released updates for 16 of their applications this month, addressing 165 vulnerabilities – almost quadruple the number of vulnerabilities as last month. The applications in question are:
· Experience Manager (AEM)
· Acrobat and Reader
· Media Encoder
· Illustrator
· After Effects
· Animate
· InDesign
· PDFL Software Development Kit (SDK)
· Connect
· Substance 3D Sampler
· Photoshop
· Substance 3D Modeler
· Bridge
· Premiere Pro
· Substance 3D Painter
· FrameMaker
Cisco
Cisco has so far released just 2 advisories in December, with the impact rating for one being High and the other being Medium. The one rated as High is a software image bypass vulnerability in products running NX-OS, mainly for Cisco switches.
Fortinet
Fortinet has addressed 8 vulnerabilities since last Patch Tuesday, with one rated as High and one as Critical. The two highest rated are both updates to previously disclosed vulnerabilities, with CVE-2024-6387 being an update to the OpenSSH regreSSHion attack published in July, and CVE-2024-47575 being an update to the missing authentication in the FortiManager fgfmd daemon published in October.
Palo Alto
Although disclosed in November with no CVE number initially, CVE-2024-0012 has subsequently been documented and is known to have been exploited in the wild. This is a critical authentication bypass vulnerability in the management web interface; with a CVSS score of 9.3, low attack complexity, no user interaction or privileges required, and being known to be actively exploited – users are advised to remediate this as soon as possible.
SAP
SAP has released 10 new security notes and 3 updates to previous security notes. 5 of these CVEs are rated “High” or “Hot News” (Very High). The products affected by the high to very high rated CVEs are:
· SAP NetWeaver AS Java
· SAP Web Dispatcher
· SAP NetWeaver Application Server ABAP and ABAP Platform
· SAP NetWeaver Administrator
Veeam
Veeam has addressed multiple vulnerabilities this month, resolving a series of critical and high-severity vulnerabilities. The updates cover the following products:
· Veeam Backup & Replication
· Veeam Agent for Microsoft Windows
· Veeam Service Provider Console
Industrial Control Systems
Any customers utilising industrial control systems (ICS) should be aware of seven security advisories regarding:
· MOBATIME Network Master Clock
· Schneider Electric EcoStruxure Foxboro DCS Core Control Services
· Schneider Electric FoxRTU Station
· National Instruments LabVIEW
Additional information
There has been widespread exploitation of ‘Cleo’ file transfer software - CVE-2024-50623
The NCSC have released their Annual Review for 2024 - NCSC Annual Review 2024
As always, users are recommended to install the latest security updates as soon as possible to protect their systems from potential threats.




